The Best Chrome Extensions & Web Tools for Designers and Creators
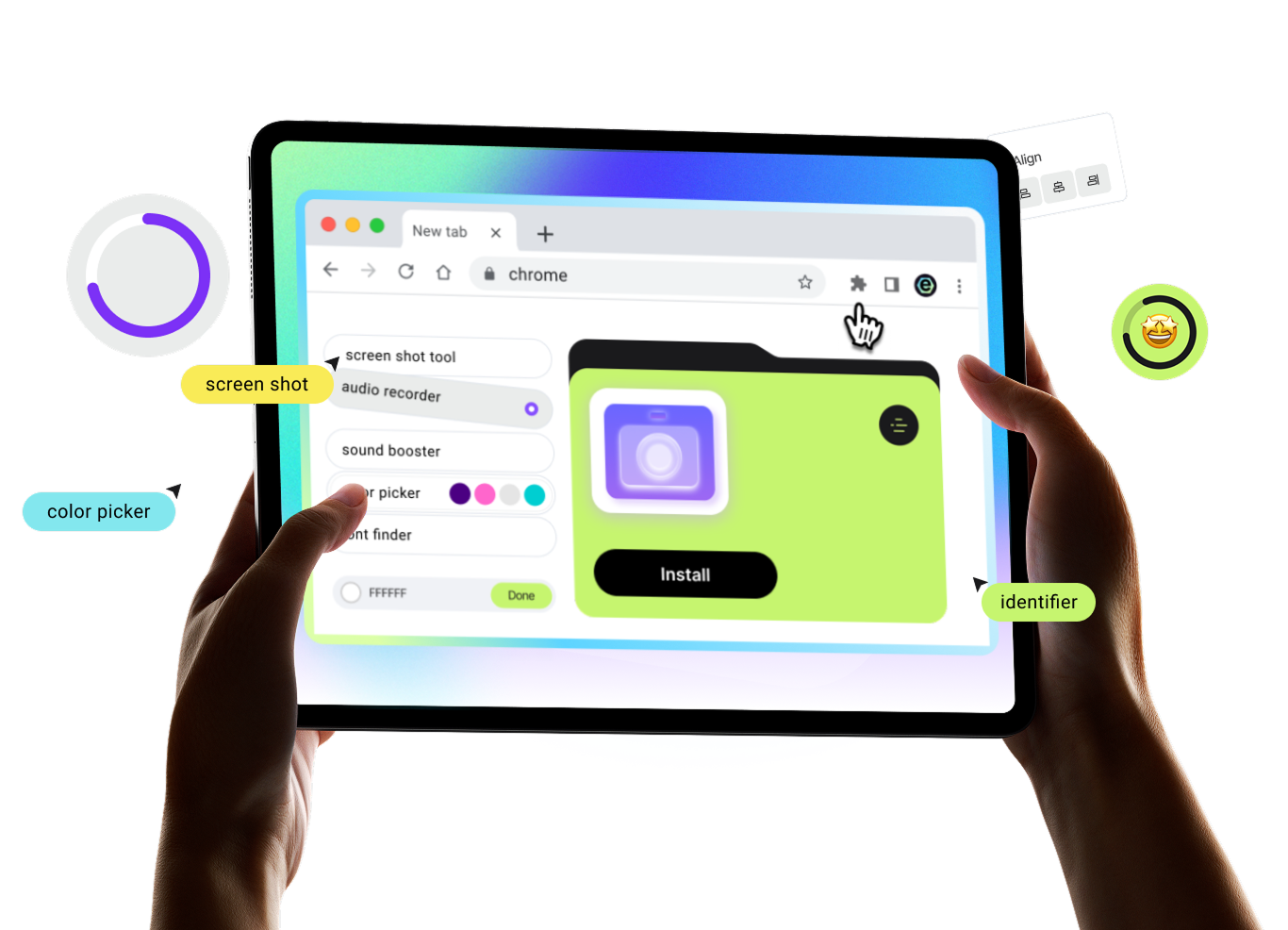
Boost your productivity with 5 powerful extensions. EpicWebTool gives you free access to screen recording, design tools, and audio enhancement — all in one place
Trusted Tools for Your Everyday Browser Workflow
Screenshots, screen and audio recording, color and font picking, and sound enhancement — all utilities are expert-tested and designed to help you complete tasks without complex setups or extra software
Stop paying for basic features
Free access to all features, no watermarks, and full privacy — the perfect alternative to Loom, ColorZilla, and other tools
Simplicity & Speed
Ready to use instantly: choose the tool you need and start working in just a few clicks


10,000+ Active Users
Reliable Performance

No Limits
No payments for basic features, no watermarks, and unlimited tool usage

Privacy First
Your data stays yours — no tracking, no data collection, and no selling to third parties



Resources & Insights
Work faster and smarter. Discover step-by-step guides, expert comparisons, and proven methods to maximize your browser’s efficiency

{ "seo_title": "Build a Secure Chrome Extension Stack for Productivity", "article_text": "<p>For many professionals, the browser is no longer just a place to read documents or check email; it is the primary workspace. Marketing campaigns are launched from tabs, code is reviewed in web apps, and research lives in browser sessions. While Chrome extensions can make this environment faster and more focused, they can also add clutter, performance issues, and unnecessary security risks. The goal is to build a secure, deliberate extension stack that improves daily work without compromising privacy.</p>\n\n<h2>Selecting and Vetting Your Browser Tools</h2>\n<p>Most productivity problems in the browser stem from friction: repetitive tasks, excessive open tabs, and constant context switching. Extensions solve these issues because they sit close to the workflow. However, extension sprawl often happens gradually, leading to a heavy and untrustworthy browser. A secure stack starts with a simple question: what job does this tool perform, and is it used frequently enough to justify installation?</p>\n\n<h3>The 5-Point Vetting Checklist</h3>\n<p>When evaluating a new extension, professionals should follow a strict vetting process to ensure data integrity and system performance. Before clicking install, review these criteria:</p>\n<ul>\n<li><strong>Permissions:</strong> Does it need access to all sites or only specific pages?</li>\n<li><strong>Publisher Identity:</strong> Is there a clear company, support page, and history?</li>\n<li><strong>User Reviews:</strong> Are there consistent patterns in user feedback?</li>\n<li><strong>Update Frequency:</strong> Has the tool been maintained recently?</li>\n<li><strong>Data Handling:</strong> Where is your browsing data being sent?</li>\n</ul>\n\n<table>\n <thead>\n <tr>\n <th>Tool Category</th>\n <th>Primary Benefit</th>\n <th>Key Vetting Factor</th>\n </tr>\n </thead>\n <tbody>\n <tr>\n <td>Tab Management</td>\n <td>Reduces RAM usage</td>\n <td>Site access limits</td>\n </tr>\n <tr>\n <td>Content Clippers</td>\n <td>Centralizes research</td>\n <td>Data storage location</td>\n </tr>\n <tr>\n <td>Security Tools</td>\n <td>Safeguards logins</td>\n <td>Publisher reputation</td>\n </tr>\n <tr>\n <td>Reading Modes</td>\n <td>Removes distractions</td>\n <td>Minimal permissions</td>\n </tr>\n </tbody>\n</table>\n\n<h2>Optimizing Your Daily Workflow</h2>\n<p>A strong extension stack usually covers a few clear categories: tab management, notes, page formatting, security, and automation. The best tools are narrow in scope and transparent about their data access. By focusing on single-purpose tools, you avoid the bloat associated with all-in-one bundles.</p>\n\n<h3>A Practical Workflow Example</h3>\n<p>Consider a professional building a research report. A secure stack facilitates this by grouping source articles with a <strong>tab manager</strong>, saving key quotes with a <strong>clipper</strong>, and using a <strong>reading mode</strong> to eliminate visual noise. Finally, a <strong>password manager</strong> handles credentials securely, ensuring that sensitive data is never stored directly in the browser's basic settings. This approach keeps the stack small while covering the entire lifecycle of information gathering.</p>\n\n<h3>Maintenance Best Practices</h3>\n<p>To keep your browser environment clean and safe, follow these long-term maintenance habits:</p>\n<ul>\n<li>Review all installed extensions on a monthly basis.</li>\n<li>Remove any tool that has not been used for 30 days.</li>\n<li>Use separate browser profiles for personal and work activities.</li>\n<li>Test new extensions in a secondary profile before full deployment.</li>\n<li>Watch for unexpected requests for updated permissions.</li>\n</ul>\n\n<p>A productive browser setup is not built by collecting the most tools; it is built by choosing a small, trusted stack that fits real workflows. If an extension saves time every day and asks only for the access it truly needs, it is a valuable asset to your professional toolkit.</p>\n\n<h4>Frequently Asked Questions</h4>\n<h4>How do I check what permissions an extension has?</h4>\n<p>In Chrome, go to Settings > Extensions > Details. This page lists all data access and site permissions granted to the specific tool.</p>\n<h4>Can too many extensions slow down my computer?</h4>\n<p>Yes. Every active extension consumes memory (RAM) and CPU cycles. Too many background processes will lead to browser lag and faster battery drain.</p>\n<h4>Is it safe to use a browser-based password manager?</h4>\n<p>Dedicated extensions from reputable security firms (like Bitwarden or 1Password) are generally safer than the browser's built-in "save password" feature.</p>\n<h4>What should I do if an extension asks for new permissions?</h4>\n<p>Investigate the update. If a simple tool suddenly asks for access to \"all website data,\" it may have been sold to a new owner or compromised.</p>", "meta_description": "Learn how to build a secure Chrome extension stack for work. Vet tools for privacy, optimize your workflow, and reduce browser clutter with our practical guide.", "image_prompt": "A modern editorial tech illustration of a clean browser window interface floating in a 3D workspace. Minimalist icons representing security, tab management, and research tools are neatly organized in the toolbar. Soft blue and silver color palette, high-end digital productivity aesthetic, no text." }

The Myth of “Popular Extensions = Safer Browsing”
Don’t assume high download counts mean high security. Learn why popular Chrome extensions can pose a risk and how to evaluate tools for a safer professional workflow.

Chrome Extensions Weekly: AI Skills and Supply Chain Security
Chrome Extensions Weekly with Lars Erik Rydberg: Discover Google’s new AI Skills, extension ownership security risks, and the final shift to Manifest V3.
Got Questions? We’ve Got Answers
Yes. You can use all core features for free — no hidden fees or trial periods.
Installation takes just seconds. Simply add the extension from the browser store — no registration or setup required.
Yes. You can easily disable or completely remove the extension in your browser settings at any time.
Yes. We follow a privacy-first approach — no recordings, videos, or personal data are sent to third-party servers without your consent.
The tool works directly in your browser and is compatible with Windows, macOS, and Chromebook — no additional software required.

You’re Just 3 Clicks Away from Better Productivity
Our step-by-step guide makes it easy to launch and use trusted tools for maximum efficiency
Step 1
Add to Chrome
Choose the tool you want and click "Install." It's free
Step 2
Pin the Icon
Click on the "Puzzle" icon in your browser and pin the icon for quick access
Step 3
Boost Workflow
Activate the extension with one click when you need it
Unlimited Browser Productivity
Whether you're recording a Google Meet call, picking colors from Dribbble, or boosting volume on Netflix — our tools are optimized for the web's most popular sites.

















